Today, April 10, 2026, one of the most trusted names in PC hardware monitoring has just become a weapon against its own users. CPUID, which is the French software company behind the world-famous system diagnostic tools CPU-Z and HWMonitor, had its official distribution infrastructure breached by hackers. The attackers quietly replaced the legitimate download links with trojanized malware-laced installers, meaning anyone who visited cpuid.com and downloaded either tool in recent days likely installed dangerous malicious software on their computer without knowing it. This is called a supply chain attack.
In this attack, instead of targeting individual users, hackers compromised the trusted source itself, turning a software update into a digital weapon delivered to thousands of unsuspecting victims simultaneously. CPU-Z alone has tens of millions of users globally. It is one of the most downloaded PC utility tools in the world, trusted by everyday enthusiasts, professional system builders, IT technicians, and original equipment manufacturers (OEMs).
HWMonitor is also equally popular; it is used to read real-time temperatures, voltages, and fan speeds across CPUs, GPUs, and hard drives. The fact that hackers chose this particular target is no accident. The more trusted a software source, the more devastating a supply chain attack becomes.
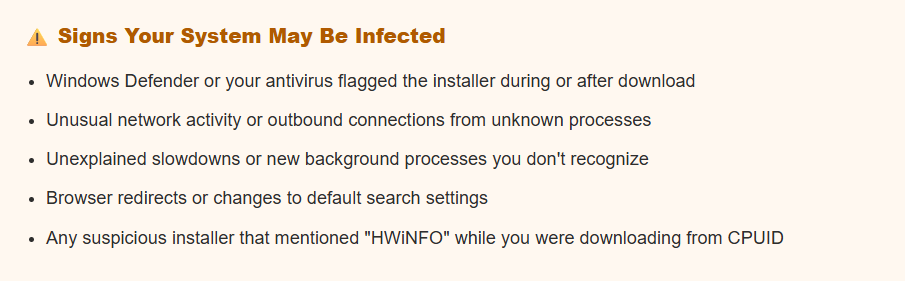
The breach first came to light through user reports on Reddit, where a PC enthusiast noticed something deeply wrong while trying to update to "HWMonitor version 1.63." The official CPUID download page was silently redirecting the user to an external server, not CPUID's own infrastructure. That server delivered a file suspiciously named "HWiNFO_Monitor_Setup.exe."
HWiNFO is a completely separate, unrelated, and legitimate hardware monitoring tool made by a different developer. Seeing that name on a CPUID download page was an immediate red flag. After observing this, community members and security researchers quickly dug deeper and confirmed the worst. The worst part is that the download link embedded on CPUID's official HWMonitor page was redirecting to an external domain that is hosted on "Cloudflare R2 storage," which is entirely outside CPUID's normal servers.
That external domain was serving a trojanized installer wrapped inside a modified "Inno Setup package," which is a technique specifically chosen to hide malicious code and block security analysis tools from detecting it. The malware security research group "vx-underground," which is one of the most respected names in malware analysis, confirmed the threat on April 10, 2026, and described what they found in striking detail.
After investigating, they found out that this is not a simple adware infection or a low-level nuisance. This malware is deeply trojanized, meaning it is disguised as something completely legitimate while hiding powerful malicious capabilities underneath. It is multi-staged, which means it executes in multiple hidden phases to avoid the detection. It operates almost entirely in-memory, leaving minimal traces on the hard drive to evade forensic tools.
It is also capable of performing "file masquerading," which means pretending to be system files and using advanced techniques to bypass "Endpoint Detection and Response" (EDR) systems and traditional antivirus tools by proxying "Windows system" functions through a .NET assembly. Most importantly, security researchers identified an active command-and-control (C2) infrastructure embedded in the malware.
This means that the infected installer is designed to phone home to a remote server that is controlled by the attackers. This allows them to deliver further payloads, steal data, or maintain persistent access to compromised systems.
Who did this?
The threat group behind this attack is not new. Researchers linked the same C2 infrastructure to a group that was previously caught distributing "trojanized" versions of "FileZilla," which is the popular FTP client, in early March 2026. These attackers have been systematically targeting trusted, widely-used software tools to maximize the number of victims.
The CPUID breach is their most impactful campaign yet, as they compromised CPU-Z and HWMonitor user base. In March 2026 alone, major tools including Axios, LiteLLM, Trivy, and Telnyx were all compromised in rapid succession, signaling that attackers have shifted strategies from targeting individual users to poisoning the major software distribution pipelines on which trusted communities rely on.
As of now, CPUID has not issued an official public statement, and their website is currently offline. The server is likely taken down either by the company itself after becoming aware of the compromise, or as a result of the attack. It remains unclear exactly how the attackers gained access to CPUID's infrastructure.
What Should We Do Immediately?
This malware operates in-memory and is engineered to evade standard antivirus detection, which means simply "not seeing a warning" does not mean your system is clean. Here are some recommended steps:
- Run a full system antivirus scan immediately. Malwarebytes Free is a reliable second-opinion scanner to use alongside Windows Defender.
- If the installer file is still present on your system, go to virustotal.com and upload it for analysis. VirusTotal scans files with 70+ antivirus engines simultaneously. This will help to confirm whether the file that was downloaded is the malicious version.
- Uninstall CPU-Z and HWMonitor if you installed them recently. Do not reinstall them from CPUID's website until the company officially confirms the issue is resolved and the site is clean.
- Change passwords for your email, banking, social media, and any accounts you accessed on the affected machine after the date of installation. It's because, this malware includes active C2 infrastructure and operates in-memory. So, there is a real risk it could have exfiltrated credentials.
- As an additional layer of protection against potential credential theft from this breach, activate 2FA on all major accounts.
- Even if cpuid.com comes back online, wait for a clear official statement from CPUID confirming the issue is fully resolved and that their installers have been verified clean.
As for CPUID's side, the company will need to take their infrastructure fully offline, audit all download links and server-side configurations, purge the malicious files. They need to restore clean versions of their installers, and issue a transparent public statement detailing what happened, what was compromised, and for how long the malicious downloads were being served.
Cybersecurity agencies and researchers are likely already examining the malware samples. Given the sophistication of this threat and its connection to the same group that hit FileZilla in March 2026, law enforcement and threat intelligence organizations will almost certainly be involved in tracking down the responsible actors.
Anyways, what are your thoughts on this current situation? Let me know in the comments, where you can also provide the latest news so I can make a breakdown of it.
Do you know that a man Jailed 28 Months After Grooming 14-Year-Old Girl He Met on Roblox. Check out for the full story in my previous article.